HIPAA Training Best Practices: Building an Effective Compliance Program for Healthcare Organizations
Compliance Armor Editorial TeamJanuary 21, 202614 min read
Share:
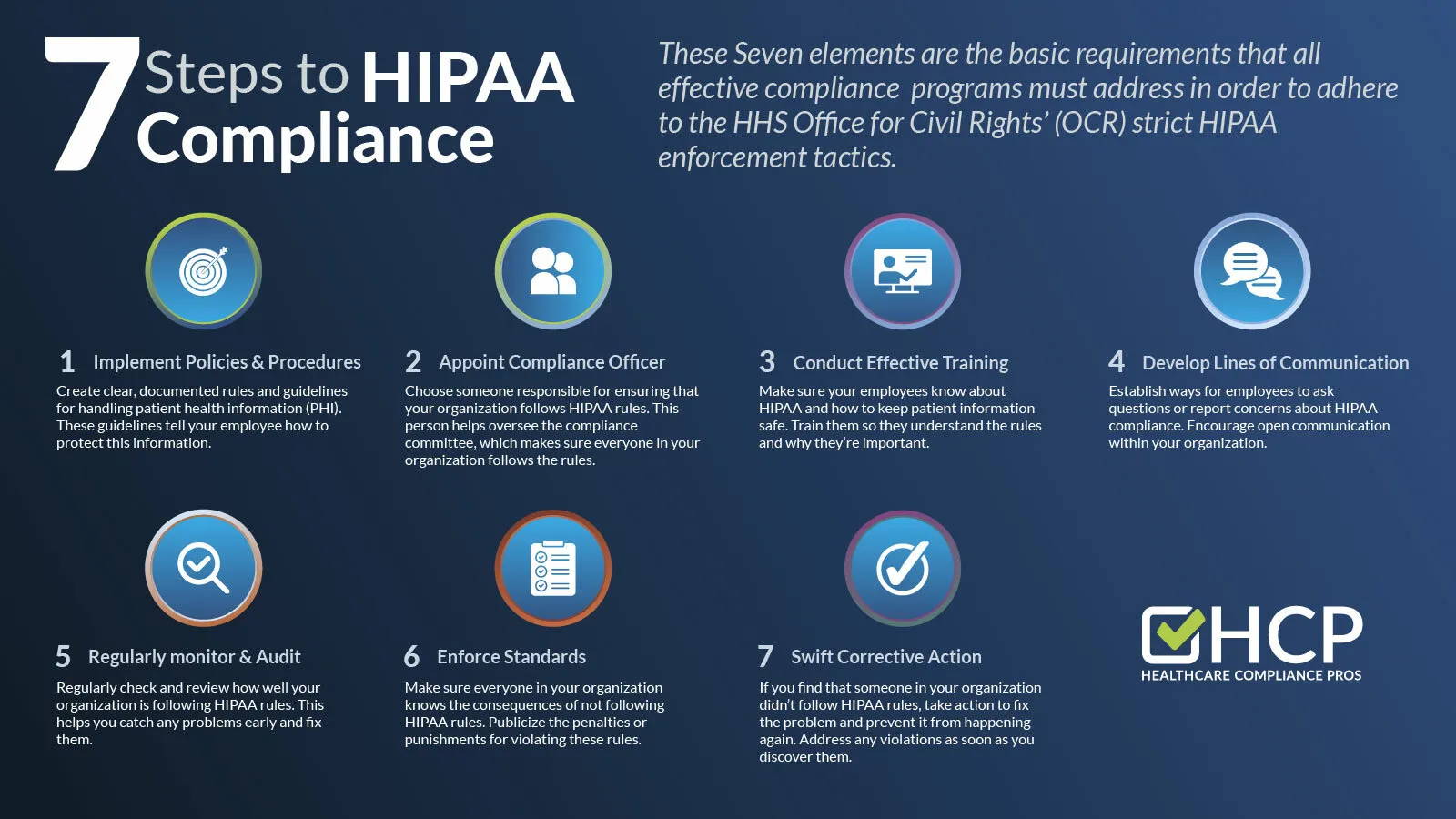
The Health Insurance Portability and Accountability Act (HIPAA) has shaped healthcare privacy and security practices for over two decades, yet organizations continue to struggle with compliance. Data breaches affecting healthcare organizations reached record levels in recent years, with the Office for Civil Rights (OCR) reporting hundreds of major incidents annually. At the heart of many compliance failures lies inadequate training. This comprehensive guide explores best practices for HIPAA training that actually works, helping healthcare organizations protect patient information while avoiding costly penalties.
## Understanding HIPAA Training Requirements
HIPAA does not prescribe a specific training curriculum or format, giving covered entities and business associates flexibility in how they educate their workforce. However, this flexibility comes with responsibility. Organizations must ensure their training programs effectively prepare employees to handle protected health information (PHI) appropriately.
### What the Regulations Actually Require
The HIPAA Privacy Rule requires covered entities to train all workforce members on policies and procedures regarding PHI as necessary and appropriate for them to carry out their functions. The Security Rule requires training for all workforce members regarding security policies and procedures. These requirements apply to employees, volunteers, trainees, and any other persons whose conduct is under the direct control of the covered entity or business associate.
Training must be provided within a reasonable period after a person joins the workforce and whenever functions are affected by material changes in policies or procedures. While HIPAA does not specify training frequency, annual refresher training has become the industry standard and is often required by state laws or contractual obligations.
### The Role of Documentation
Documentation serves two critical purposes in HIPAA training. First, it demonstrates compliance to regulators during audits or investigations. Second, it provides evidence that employees received training, which can be important in disciplinary proceedings or litigation.
Maintain records of training content, attendance, and completion dates. Many organizations also require employees to acknowledge their understanding of training content and their obligation to comply with organizational policies.
## Designing Effective HIPAA Training Programs
Effective HIPAA training goes beyond checking a compliance box. It changes behavior, reduces risk, and creates a culture of privacy and security awareness throughout the organization.
### Know Your Audience
Different workforce members have different training needs based on their roles and access to PHI. A registration clerk who collects patient demographic information needs different training than a nurse who accesses clinical records or an IT administrator who manages systems containing PHI.
Role-based training addresses these differences by providing baseline training for all workforce members plus specialized modules for specific roles. This approach ensures everyone understands fundamental privacy and security principles while those with greater access or responsibility receive more detailed instruction.
### Make Training Relevant and Practical
Abstract discussions of regulatory requirements rarely change behavior. Effective training connects HIPAA requirements to employees' daily work through realistic scenarios, examples from their specific work environment, and clear guidance on handling common situations.
Consider the difference between telling employees they must protect PHI and showing them how to verify caller identity before releasing information over the phone, how to position computer screens to prevent unauthorized viewing, and what to do if they receive a misdirected fax containing patient information. Practical guidance makes compliance actionable.
### Use Engaging Delivery Methods
Compliance training has a reputation for being boring, but it does not have to be. Modern training approaches use interactive elements, video content, gamification, and scenario-based learning to maintain engagement and improve retention.
Interactive scenarios that require employees to make decisions and see the consequences of their choices prove particularly effective. When employees experience the impact of a wrong decision in a safe training environment, they are more likely to make the right decision in real situations.
### Address Common Misconceptions
Many HIPAA violations stem from misunderstandings about what the regulations require or allow. Effective training addresses common misconceptions directly.
For example, many employees believe they cannot discuss patients with family members under any circumstances, when in fact HIPAA permits such disclosures when the patient is present and does not object, or when the provider reasonably infers the patient would not object. Others believe HIPAA prohibits all uses of patient information for marketing, when the regulations actually permit certain communications.
By addressing these misconceptions, training helps employees understand the nuances of HIPAA compliance rather than applying overly restrictive interpretations that can interfere with patient care.
## Essential HIPAA Training Topics
While training content should be tailored to organizational needs and workforce roles, certain topics should be addressed in every HIPAA training program.
### Privacy Rule Fundamentals
All workforce members need to understand the basic framework of the Privacy Rule, including what constitutes PHI, the minimum necessary standard, permitted uses and disclosures, patient rights regarding their information, and the organization's privacy policies and procedures.
Training should explain that PHI includes any individually identifiable health information, whether in electronic, paper, or oral form. Employees should understand that PHI extends beyond medical records to include billing information, appointment schedules, and even the fact that an individual is a patient.
### Security Rule Essentials
The Security Rule applies specifically to electronic PHI (ePHI), requiring administrative, physical, and technical safeguards. Training should cover password management and authentication, workstation security and screen locks, mobile device security, email and messaging security, physical security of devices and media, and incident reporting procedures.
Employees should understand their role in maintaining security, including recognizing and reporting potential security incidents, protecting their credentials, and following organizational security policies.
### Breach Notification Requirements
When breaches occur, timely notification is essential. Training should ensure employees understand what constitutes a breach, their obligation to report suspected breaches immediately, the organization's breach response procedures, and the potential consequences of unreported breaches.
Early detection and reporting of breaches can significantly reduce their impact and demonstrates good faith compliance efforts to regulators.
### Social Engineering and Phishing Awareness
Social engineering attacks, particularly phishing, represent a leading cause of healthcare data breaches. Training should help employees recognize phishing emails and messages, verify requests for information or access, respond appropriately to suspicious communications, and report potential social engineering attempts.
Regular phishing simulations can reinforce training and identify employees who need additional education.
### Social Media and Communication
The intersection of social media and healthcare privacy creates significant risks. Training should address appropriate use of social media in professional contexts, prohibition on posting patient information, risks of discussing work on personal social media, and organizational policies on social media use.
Even well-intentioned posts can violate HIPAA if they contain enough information to identify a patient, even without using names.
### Business Associate Requirements
Organizations that work with business associates must ensure their workforce understands these relationships. Training should cover what business associates are, how to identify potential business associate relationships, the requirement for business associate agreements, and appropriate information sharing with business associates.
Employees who engage vendors or share information with external parties need particular attention to business associate requirements.
## Training Delivery Methods
Organizations can deliver HIPAA training through various methods, each with advantages and limitations.
### Online Training
Online training offers flexibility, consistency, and scalability. Employees can complete training at convenient times, and organizations can easily track completion. Online platforms can incorporate interactive elements, videos, and assessments that enhance learning.
However, online training requires self-motivation and may not provide opportunities for questions or discussion. Some employees may rush through content without genuine engagement.
### In-Person Training
In-person training allows for interaction, questions, and discussion. Trainers can adapt content based on audience reactions and address specific concerns. Group training can also build shared understanding and commitment to compliance.
The limitations include scheduling challenges, inconsistent delivery across sessions, and higher costs for trainer time and facilities.
### Blended Approaches
Many organizations combine online and in-person elements. For example, employees might complete foundational training online, then participate in department-specific discussions led by supervisors. This approach captures the benefits of both methods while mitigating their limitations.
### Just-in-Time Training
Beyond formal training programs, organizations can provide just-in-time training through job aids, quick reference guides, and readily accessible policy information. When employees encounter unfamiliar situations, they can quickly find guidance without searching through lengthy policy documents.
## Measuring Training Effectiveness
Completing training does not guarantee compliance. Organizations should measure whether training actually changes behavior and reduces risk.
### Knowledge Assessments
Post-training assessments measure whether employees understood and retained training content. Assessments should test practical application, not just recall of facts. Scenario-based questions that require employees to apply knowledge to realistic situations provide better insight than simple true/false questions.
Track assessment results over time to identify topics that need reinforcement and employees who may need additional training.
### Behavioral Indicators
Observable behaviors indicate whether training translates to practice. Monitor indicators such as clean desk compliance, screen lock usage, badge tailgating incidents, phishing simulation results, and incident reports.
Improvements in these indicators suggest training is working. Persistent problems indicate areas needing attention.
### Incident Analysis
When incidents occur, analyze whether training gaps contributed. If employees consistently make the same mistakes, training may not adequately address those situations. Use incident data to continuously improve training content.
### Employee Feedback
Employees can provide valuable insight into training effectiveness. Survey employees about training relevance, clarity, and applicability. Ask what additional training they need and what situations they find confusing.
## Building a Culture of Compliance
Training alone cannot ensure HIPAA compliance. Organizations must build a culture where privacy and security are valued and practiced at all levels.
### Leadership Commitment
Leadership sets the tone for organizational culture. When leaders visibly prioritize privacy and security, employees follow. When leaders cut corners or dismiss compliance concerns, employees receive a different message.
Leaders should participate in training, discuss privacy and security in organizational communications, and ensure adequate resources for compliance programs.
### Accountability
Clear accountability reinforces training. Employees should understand that compliance is part of their job responsibilities and that violations have consequences. Consistent enforcement of policies demonstrates that the organization takes compliance seriously.
### Recognition
Recognize employees who demonstrate strong compliance behaviors. Positive reinforcement encourages continued compliance and signals organizational values to others.
### Open Communication
Employees should feel comfortable asking questions and reporting concerns without fear of retaliation. An environment where employees hide mistakes or avoid raising issues creates significant risk.
## Special Training Considerations
Certain situations require additional training attention.
### New Employee Onboarding
New employees should receive HIPAA training before accessing PHI. The onboarding period sets expectations and establishes habits that persist throughout employment. Do not delay training or allow access before training completion.
### Role Changes
When employees change roles, evaluate whether additional training is needed. A promotion from administrative to clinical responsibilities, for example, may require training on clinical documentation and access to more sensitive information.
### Incident Response
After incidents, provide targeted training to address the specific issues involved. If a breach resulted from a phishing attack, reinforce phishing awareness. If it resulted from improper disposal, address media sanitization procedures.
### Remote Work
Remote work creates unique privacy and security challenges. Training should address securing home work environments, protecting information during video calls, using approved tools and avoiding shadow IT, and reporting incidents when working remotely.
### Temporary and Contract Workers
Temporary staff and contractors need HIPAA training appropriate to their roles. Do not assume that because someone is temporary, they need less training. Their access to PHI creates the same risks as permanent employees.
## Frequently Asked Questions
**How often should HIPAA training be conducted?**
While HIPAA does not specify training frequency, annual training has become the industry standard. Some states require annual training by law, and many contracts and accreditation standards also require it. Beyond formal annual training, provide ongoing reinforcement through newsletters, reminders, and just-in-time resources.
**Who needs HIPAA training?**
All workforce members who have access to PHI or who could affect the privacy or security of PHI need training. This includes employees, volunteers, students, trainees, and contractors. Even employees who do not directly handle PHI, such as maintenance staff who might see information while working in clinical areas, need basic awareness training.
**How long should HIPAA training take?**
Training length should be appropriate to the content and audience. Basic awareness training might take 30 to 60 minutes, while comprehensive training for employees with significant PHI access might take several hours. Role-specific modules add to baseline training time. Focus on effectiveness rather than arbitrary time requirements.
**Can we use the same training every year?**
While core concepts remain consistent, training should be updated to address new threats, regulatory changes, and organizational policy updates. Using identical training year after year reduces engagement and may not address current risks. At minimum, update examples and scenarios annually.
**What documentation do we need to maintain?**
Maintain records of training content, including materials and any updates. Document who completed training and when. Keep signed acknowledgments if your organization requires them. Retain training records for at least six years, as required for HIPAA documentation generally.
**How do we train employees who do not use computers?**
Not all healthcare workers have regular computer access. Provide alternative training methods such as in-person sessions, printed materials, or video presentations. Ensure these employees receive the same quality training as those who complete online modules.
**What are the penalties for inadequate training?**
HIPAA violations can result in civil monetary penalties ranging from $100 to $50,000 per violation, with annual maximums up to $1.5 million per violation category. Criminal penalties can reach $250,000 and imprisonment. Beyond regulatory penalties, breaches can result in lawsuits, reputational damage, and loss of patient trust.
**How do we handle employees who fail training assessments?**
Employees who fail assessments should receive additional training and reassessment. Repeated failures may indicate the need for different training approaches or, in some cases, role reassignment. Document remediation efforts.
## The Cost of Inadequate Training
The consequences of inadequate HIPAA training extend beyond regulatory penalties. Consider the full impact of compliance failures.
### Financial Costs
OCR settlements and penalties regularly reach millions of dollars for serious violations. Legal defense costs, breach notification expenses, credit monitoring for affected individuals, and remediation efforts add to the financial burden. Organizations may also face lawsuits from affected patients.
### Operational Disruption
Breach investigations consume significant staff time and attention. Organizations may need to engage forensic investigators, legal counsel, and public relations consultants. Normal operations suffer while the organization responds to the incident.
### Reputational Damage
Healthcare organizations depend on patient trust. Breaches damage that trust and may cause patients to seek care elsewhere. Negative publicity can persist long after the incident is resolved, affecting patient volume and revenue.
### Employee Impact
Employees involved in breaches may face disciplinary action, termination, or even personal liability in egregious cases. The stress of investigations and potential consequences affects morale and productivity.
## Investing in Effective Training
Given the costs of compliance failures, investment in effective training represents sound risk management. Quality training programs cost a fraction of potential breach expenses while significantly reducing risk.
When evaluating training options, consider content quality and currency, engagement and interactivity, customization capabilities, tracking and reporting features, and vendor expertise and support.
The cheapest training option is rarely the best value if it fails to change behavior and reduce risk.
## Conclusion
HIPAA training is not merely a regulatory requirement but a critical component of protecting patient privacy and organizational interests. Effective training programs combine relevant content, engaging delivery, and ongoing reinforcement to create lasting behavior change.
Organizations that treat training as a check-the-box exercise expose themselves to significant risk. Those that invest in quality training, measure its effectiveness, and build a culture of compliance position themselves for success in an increasingly challenging regulatory environment.
Start by assessing your current training program against the best practices outlined in this guide. Identify gaps and opportunities for improvement. Engage leadership in supporting a culture of compliance. And remember that training is not a one-time event but an ongoing process of education, reinforcement, and continuous improvement.
Your patients trust you with their most sensitive information. Effective HIPAA training helps you honor that trust.

